-
RECOVERY SOFTWARE
-
Windows Recovery
Windows Recovey Software
Applicable For:
- Accidently formated drives
- FAT16 / FAT32 / NTFS Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Windows Data Recovery Software
Disk Doctors Windows Data Recovery is much more then an simple undelete software or a file recovery program. Its versatility begins when other software fails to recover or even is not able to display data... Read more >>
Regular Price: $129.97Applicable For:
- Accidently formated drives
- Windows, Mac, Linux and UNIX Partitions
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Data Recovery Suite (for Win)
Disk Doctors Windows Data Recovery is much more then an simple undelete software or a file recovery program. Its versatility begins when other software fails to recover or even is not able to display data...Read more >>
Regular Price: $249.97Applicable For:
- Accidently formated drives
- NTFS, NTFS5 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
NTFS Data Recovery Software
Use Disk Doctors NTFS Data Recovery software to recover data from NTFS, NTFS5, drives as well as it supports recovery from dynamic drives created on NT/2000/XP/2003 platforms. Recovering data using ...Read more >>
Regular Price: $89.97Applicable For:
- Accidently formated drives
- FAT16, FAT32 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
FAT Data Recovery Software
Disk Doctors FAT Data Recovery Software will of course recover lost or damaged data on any computer utilizing the Windows File Allocation Table (FAT16, FAT32) systems. It supports file recovery ...Read more >>
Regular Price: $79.97Applicable For:
- Accidently formated drives
- File system independent
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Photo Recovery Software
Disk Doctors Photo Recovery (Win) can recover data from all camera flash memory cards including Compact Flash Card (CF), Smart Media Card, Secure Digital Card (SD), Multi-Media... Read more >>
Regular Price: $49.97Applicable For:
- Accidently formated drives
- FAT16 / FAT32 / NTFS Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Instant File Recovery Software
Disk Doctors Instant File Recovery Software will easily recover deleted files emptied from your Windows Recycle Bin. it will also allow you to quickly recover files lost due to errors such as accidental formatting...Read more >>
Regular Price: $69.97Recover Files Deleted....
- Even after emptied recycle bin.
- Bypassing recycle bin.
- Using DOS command prompt.
- After pressing Shift+Delete key
- When Move or Cut command has been used.
- by other applications or by viruses.
Undelete Recovery Software
Disk Doctors Undelete is the world's fastest and most reliable undelete software. It utilizes a very easy to operate interface and contains powerful functions that allow anyone...Read more >>
Regular Price: $49.97 -
Mac Recovery
MAC Recovey Software
Applicable For:
- Accidently formated drives
- HFS, HFS+, HFSX Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Mac Data Recovery Software
Disk Doctors Mac Data Recovery software recovers lost and deleted data from HFS+, HFSX file systems on Mac OS X. Data loss is not a strange term for people working on Mac...Read more >>
Regular Price: $179.97Applicable For:
- Accidently formated drives
- Windows, Mac, Linux and UNIX Partitions
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Data Recovery Suite (for Mac)
Disk Doctors Windows Data Recovery is much more then an simple undelete software or a file recovery program. Its versatility begins when other software fails to recover or even is not able to display data...Read more >>
Regular Price: $259.97Applicable For:
- Accidently formated drives
- NTFS, NTFS5 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
NTFS Data Recovery Software (for Mac)
Use Disk Doctors NTFS Data Recovery software to recover data from NTFS, NTFS5, drives as well as it supports recovery from dynamic drives created on NT/2000/XP/2003 platforms. Recovering data using ...Read more >>
Regular Price: $99.97Applicable For:
- Accidently formated drives
- FAT16, FAT32 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
FAT Data Recovery Software
Disk Doctors FAT Data Recovery Software will of course recover lost or damaged data on any computer utilizing the Windows File Allocation Table (FAT16, FAT32) systems. It supports file recovery ...Read more >>
Regular Price: $89.97Applicable For:
- Accidently formated drives
- File system independent
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Photo Recovery Software (for Mac)
Disk Doctors Photo Recovery (MAC) can recover data from all camera flash memory cards including Compact Flash Card (CF), Smart Media Card, Secure Digital Card (SD), Multi-Media... Read more >>
Regular Price: $69.97 -
Photo Recovery
Applicable For:
- Accidently formated drives
- File system independent
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Photo Recovery Software
Disk Doctors Photo Recovery (Win) can recover data from all camera flash memory cards including Compact Flash Card (CF), Smart Media Card, Secure Digital Card (SD), Multi-Media... Read more >>
Regular Price: $49.97Applicable For:
- Accidently formated drives
- File system independent
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Photo Recovery Software (for Mac)
Disk Doctors Photo Recovery (MAC) can recover data from all camera flash memory cards including Compact Flash Card (CF), Smart Media Card, Secure Digital Card (SD), Multi-Media... Read more >>
Regular Price: $69.97 -
Phone & Tablet
Phone & Tablet Recovery
Applicable For:
- Recovering, accidentally deleted photos, videos or other files
- Support for all popular files types
- Efficient and fast recovery of files
- Evaluate recovery results with preview option
- Partitions / Volumes are missing or corrupted
- Open iPhone 2G, iPhone 3G, iPhone 3GS, iPhone 4 and iPad1
iOS Data Recovery Software
Disk Doctors iOS Recovery, makes use of low level flash file system.Low level flash file system keeps multiple versions of the same file....Read more >>
Regular Price: $49.97 Discount: $20.00" You Pay: $29.97Applicable For:
- Accidently formated drives
- Windows, Mac, Linux and UNIX Partitions
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
iOS Data Recovery Software
Disk Doctors iOS Recovery, makes use of low level flash file system.Low level flash file system keeps multiple versions of the same file...Read more >>
Regular Price: $69.97 Discount: $40.00" You Pay: $29.97Applicable For:
- Recover accidently deleted photos, videos and other files
- Support for all popular file types
- Evaluation of recovery results is assured with preview option
- Support Windows & Mac
- Supports SD-Card mounted as USB Storage
- Does NOT support SD-Card mounted as MTP or PTP
Android Data Recovery Software
Disk doctors Android Data Recovery Software Support recovering, accidentally deleted photos, videos or other files. This software can be used on Windows and Mac ...Read more >>
Regular Price: $34.97 Discount: $5.00" You Pay: $29.97Applicable For:
- Accidently formated drives
- FAT16, FAT32 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Android Data Recovery Software
Disk doctors Android Data Recovery Software Support recovering, accidentally deleted photos, videos or other files. This software can be used on Windows and Mac ...Read more >>
Regular Price: $34.97 Discount: $5.00" You Pay: $29.97 -
E-Mail Recovery
Applicable For:
- Deleted messages, contacts and notes.
- Fixing corruption inside the .dbx file header.
- Corruption due to compacting of a .dbx file.
- Corruption caused due to over sized .dbx file.
- Corruption of .dbx files when used over a network.
Email Recovery Software
Disk Doctors Email Recovery (.dbx) software is a tool designed for recovering accidentally deleted Outlook Express email messages from any "dbx / mbx" archive or to repair ...Read more >>
Regular Price: $69.97 Discount: $20.00" You Pay: $49.97}Applicable For:
- Deleted messages, contacts and notes.
- Fixing corruption inside the .pst file header.
- Corruption due to compacting of a .pst file.
- Corruption caused due to over sized PST file.
- Corruption of .PST files when used over a network.
Outlook Mail Recovery
Disk Doctors Outlook Mail Recovery (.pst) is a powerful and efficient Microsoft Outlook recovery tool. The primary function is recovery of (.pst) files for Microsoft Outlook... Read more >>
Regular Price: $149.97Applicable For:
- Easy Outlook PST file migration
- Backup Outlook PST File
- Move the file to desired Laptop/PC
- Restore emails with original settings
Smart Outlook Email Backup
Use Disk Doctors Smart E-mail Backup to Migrate and Backup Outlook Emails & settings. Migrate your older version of Microsoft Outlook to newer version OR migrate from Windows XP / Vista to...Read more >>
Regular Price: $39.97 -
UNIX Recovery
Applicable For:
- Accidently formated drives
- Ext-2, EXT-3, Ext-4 Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
Linux Data Recovery Software
Disk Doctors Linux Data Recovery software is a user-friendly tool that allows you to recover data from the Linux Ext2, Ext3 & Ext4 File System created from on any Linux Distribution ...Read more >>
Regular Price: $99.97Applicable For:
- Accidently formated drives
- UFS Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
UNIX Data Recovery Software
Disk Doctors UNIX Recovery (Solaris) is simple yet powerful and easy to use application for UFS file system supported by Sun Solaris. The software has been designed to provide... Read more >>
Regular Price: $299.97Applicable For:
- Accidently formated drives
- XFS Partition
- Virus infected partition
- Inaccessible / Corrupt Partition
- Deleted Files/Data
- Partially over written partition
- Files emptied from Recycle Bin
XFS Data Recovery Software
Disk Doctors XFS Data Recovery software works for XFS file system only and is not targeted to any particular operating system due to wide support of XFS with various UNIX and Linux operating systems...Read more >>
Regular Price: $199.97 -
VM-XEN Recovery
Applicable For:
- Recovering, Citrix XenServer VMs
- Recovering VHDs from Citrix XenServer
- Support saving VHDs as mountable VHD file
- Support saving Raw partition as image file
- Deals with variety of crashed virtual machine
VM Recovery (XenServer)
Support recovering, Citrix XenServer VMs, Support recovering VHDs from Citrix XenServer, Support saving VHDs as...Read more >>
Regular Price: $299.97
-
Windows Recovery
-
SYSTEM UTILITIES
-
Drive Clone
Applicable For:
- Create sector by sector drive copy
- Create drive image
- Restore Drive image
- Perform surface Scan to locate bad blocks
- Excelent Utilty in software toolbox
Drive Cloning Software
Drive Cloning, can help you make a clone of your hard drive or make a disk image that you can use to restore your data. Drive Image's clone option creates an exact replica of the drive. Cloning is great way to ...Read more >>
Regular Price: $39.97 -
Drive Manager
Applicable For:
- Precisely monitors your Hard Drive Functions
- Surface Scan option finds bad blocks and sectors
- Check Drive and CPU temperature
- Predict potential Failures
- Make a clone of your Hard Drive
- Make a Disk Image to restore your data later
Drive Manager Software
Disk Doctors Drive Manager in itself holds a number of recovery methods and techniques which makes it unique and robust recovery software. Another very important feature of this tool is ...Read more >>
Regular Price: $39.97
-
Drive Clone
-
DATA SECURITY
-
File Shredder
Applicable For:
- Eliminates files, folders and deleted data
- FAT16 / FAT32 / NTFS Partition
- Single Click" shreddind of files and folders
- Inbuilt Scheduler to schedule shredding tasks
- Wipe Disks clean before donating your computer
- Removed data permanently by shredding unused space
File Shredder Utility
When a file is deleted either by simple delete or by using Shift+Del keys, it is not completely wiped out from the computer. Windows Operating System just removes the deleted file entry from the directory...Read more >>
Regular Price: $49.97 -
Data Sanitizer
Applicable For:
- Securely erase Data files
- Wipe the Drive beyond Recovery
- Fast Zero Overwrite
- Random Overwrite
- Meets following Standards...
- US Navy, NAVSO P-5239-26- RLL
- US Department of Defence(DoD 5220.22-M)
- DoD Standards 5220.28 STD
- North Atlantic Treaty Organization-NATO Standard
- Peter Gutmann Secure Deletion
Data Sanitizer Software
Disk data wipe or erasing ensures privacy. Operating system's default delete function does not delete the entire file. To erase the drive beyond recovery certain software procedures are necessary...Read more >>
Regular Price: $39.97 -
Crypto - Secure Backup & Recovery
Applicable For:
- Secure Data Backup & Recovery
- Swift Startup and easy to use interface
- Craetes Password Protected Repository Folder in your Flash Drive and on yourt Dard Drive
- 128 and 256 AES encryption for Data Security
- Esay restore process of Backup files
Disk Doctors Drive SOS
Drive SOS, part of the Drive Manager package, is designed to precisely monitor your hard drive functions, predict potential failures and get the most out of your drive. SOS is your first line of defense in the event of a potential drive failure. If Drive SOS does predict a hard drive failure, you will need to make a backup and replace the damaged hard driveRead more >>
Regular Price: $0.00
-
File Shredder
- RECOVERY SERVICES
- BUNDLE OFFERS
- STORE
-
SUPPORT
-
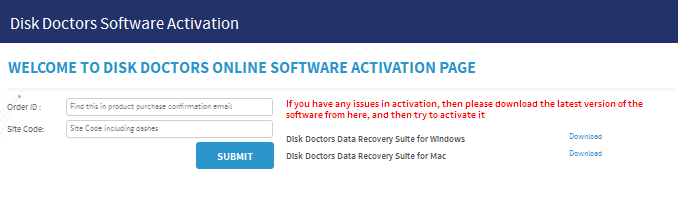
Product Activation

Product Activation
Disk Doctors online activation system helps you to activate your's software copy online and without any hassel. You just need to enter your purchase order ID that is emailed to you when you purchase the software first time and the.... -
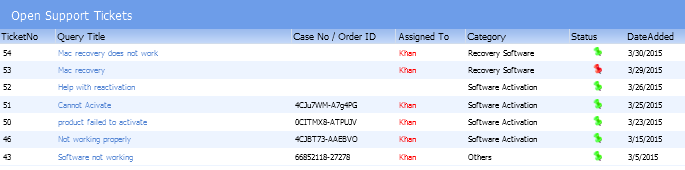
Submit a Ticket

Disk Doctors Help Desk
Disk Doctors online help desk is availabe for the cupport our valuable customers 24/7. Submit your ticket to our help desk and get an immediate responce from our support team .... -
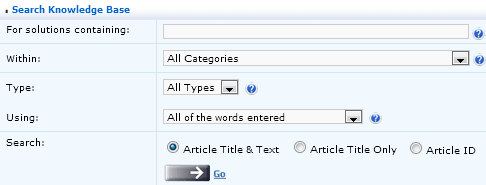
Knowledge Base
Knowledge Base
Search for your question or problem in our extensive knowledge base section using topics and keywords. The Knowledge Base has many product specific articles, created by Disk Doctors Support professionals who have resolved issues for customers. It is regularly updated, expanded, and refined to ensure that you have access to the very latest information. - Product Tutorials
- FAQ's
-
Product Activation
Privacy Policy
- Home
- Privacy Policy
We know that you care how your information is used, and we appreciate your trust that we will use it carefully and sensibly. This notice describes our privacy policy.
By visiting www.diskdoctors.net or its sub pages, you are accepting the privacy policy described below.
1. What Personal Information Do We Collect?
Information You Provide. We receive and store information you enter. For example, when you search for or buy a product or service, or when you supply information such as your address, phone number or credit card. You can choose not to provide certain information, but then you might not be able to take advantage of some of our features. We use the information that you provide for such purposes as responding to your requests, customizing future browsing for you, improving our website, and communicating with you.
Cookies. Like many websites, we use "cookies".
Cookies are small programs that we transfer to your hard drive that allow us to
recognize you and to provide you with a customized browsing experience. If
you do not want us to use cookies, you can easily disable them by going to the toolbar
of your web browser, and clicking on the “help” button. Follow
the instructions that will prevent the browser from accepting cookies, or set the
browser to inform you when you receive a new cookie. In addition, you may
visit this and other websites anonymously through the use of utilities provided
by other private companies.
Other Information: Every computer has an IP (Internet Protocol)
address. IP addresses of computers used to visit this site are noted.
In addition, we automatically collect other information such as browser types, operating
systems, and the URL addresses of sites clicked to and from this site.
Information from Other Sources. We might receive information about you from other sources and add it to our account information. This may include updated delivery and address information from our shippers or other sources so that we can correct our records and deliver your next purchase or communication more easily.
2. How Do We Use Your Information?
Customized Browsing. We use your information to better serve
you by providing a customized browsing experience.
Agents. We employ other companies and individuals to perform functions
on our behalf. Examples include delivering packages, sending postal mail and e-mail,
and processing credit card payments. They have access to personal information needed
to perform their functions, but may not use it for other purposes.
Special Offers. We may send you special offers from time
to time, unless you choose to “opt-out” of receiving such offers.
In addition, we may also send you special offer from other companies, you will
be provided a facility to “opt-out”.
Business Transfers. As we continue to develop our business, we
might sell or buy stores or assets. In such transactions, customer information generally
is one of the transferred business assets. Also, in the unlikely event that we are
acquired, customer information will be one of the transferred assets.
Law Enforcement. If we receive a lawful court order to release account or other personal information then we will comply with the law. We will also release information when necessary to protect the life, safety or property of others. This includes exchanging information with other companies and organizations for fraud protection and credit risk reduction.
3. How Do We Protect the Security of Your Information?
We work to protect the security of your information during transmission by using
Secure Sockets Layer (SSL) software, which encrypts information you input.
We use encryption to protect your information contained in our customer list.
We use a firewall to protect against unlawful intrusion.
We limit access to your information on a “need to know” basis.
We reveal only the last four digits of your credit card numbers when confirming an order. Of course, we transmit the entire credit card number to the appropriate credit card company during order processing.
It is important for you to protect against unauthorized access to your password and to your computer. Be sure to sign off when finished using a shared computer.
No system can guarantee absolute security, just as the finest lock can not guarantee physical security. However, we take every reasonable precaution to assure that your data is secure.
4. Your Choice: Opt-in or Opt-out.
It is your choice whether to receive emails or special offers from us or others. You will be provided with a facility to “opt out” of these emails.
5. Other Websites
Various Web sites may be linked to from this site. If you are transferred to another site from this site, your privacy depends on the policy of that site. We strongly urge you to check their privacy policy. Not all sites guarantee that they will not share your personally identifiable information with others
6. Contact Us
If you would like to learn more about our privacy policy, or to access your personally identifiable information contained on our website, you may contact us at [email protected] . You will be to provide identifier information to assure that this information is not released to others.
7. Policy Changes
We reserve the right to modify this policy in the future. If we do so, notice will be posted on our website and the Policy page will show the changes.








 Installation Guide
Installation Guide